Mikrotik – QoS (Quality of Service) para VoIP
Howto anterior
Este howto puede considerarse una segunda parte de Livebox Orange detrás de router neutro Mikrotik con VoIP funcionando
Objetivos
- Garantizar un mínimo de ancho de banda de conexión a Internet para VoIP
Diferencias con otros howtos
- Basada en red 192.168.1.1/24 (se conserva esta porque se heredó de una red de Teléfonica / Movistar ADSL)
- En la medida de lo posible se explican los diferentes pasos realizados y no es un simple «Copiar y pegar todos los comandos»
- Se conecta al Microtik mediante ssh en lugar de con winbox o utilidades similares
- No se sacaran passwords de SIP del Livebox para sustituir por un dispositivo VoIP
Materiales
- Mikrotik CRS125-24G-1S-RM (También aplicable a Mikrotik 750 y otros modelos)
- Dispositivo VoIP (Opcional si podemos usar el PC)
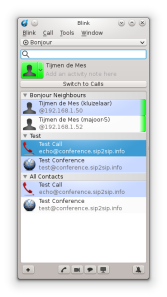
Cómo conectarse al Microtik
- Sólo podemos conectarnos por cable (este modelo no tiene Wifi). Aún así, aunque tuviera wifi lo recomendable es conectarse por cable.
- El PC lo tendremos que configurar, para mayor comodidad, para trabajar con ip estática y en el mismo rango que el de Microtik.
- Abrimos un cliente SSH (putty en Windows) y lo apuntamos a la ip (que tenga en ese momento el Microtik) con el usuario: admin . Por ejemplo: admin@192.168.88.1 .
- Nos conectamos al puerto 2
Describiremos cómo configuramos el Mikrotik.
Configuración de red del PC
Para conectarse al router tenemos que configurar la red de nuestro PC para interactuar con él. En nuestro caso la ip del Mikrotik es: 192.168.1.1 .
IP: 192.168.1.10
Mascara de red: 255.255.255.0
service network-manager stop
ifconfig eth0 192.168.1.10 netmask 255.255.255.0
Conexión inicial a Mikrotik
Nos conectamos al router por ssh en el puerto 3.
ssh -p 22 admin@192.168.1.1
Aceptamos la key.
Nos aparece algo parecido a:
MMM MMM KKK TTTTTTTTTTT KKK
MMMM MMMM KKK TTTTTTTTTTT KKK
MMM MMMM MMM III KKK KKK RRRRRR OOOOOO TTT III KKK KKK
MMM MM MMM III KKKKK RRR RRR OOO OOO TTT III KKKKK
MMM MMM III KKK KKK RRRRRR OOO OOO TTT III KKK KKK
MMM MMM III KKK KKK RRR RRR OOOOOO TTT III KKK KKK
MikroTik RouterOS X.YY.Z (c) 1999-2016 http://www.mikrotik.com/
[?] Gives the list of available commands
command [?] Gives help on the command and list of arguments
[Tab] Completes the command/word. If the input is ambiguous,
a second [Tab] gives possible options
/ Move up to base level
.. Move up one level
/command Use command at the base level
[admin@MikroTik] >
Pulsamos cualquier tecla para continuar.
Ahora por comodidad vamos a hacer un dump de la configuración actual.
/export file=dump_prevoip_20171030
Con scp (desde el PC) podemos obtener este dump.
scp -P 22 admin@192.168.1.1:dump_prevoip_20171030.rsc .
Mangle del tráfico hacia centralita IP
Marcaremos los diferentes tráficos VoIP para que luego puedan ser priorizados.
La direcci\’on de la centralita en este ejemplo va a ser: 192.168.1.246 . La centralita está dentro de nuestra red local y conecta a un trunk sip externo.
Así pues hemos de priorizar tanto el tráfico que va hacía ella como el que sale de ella.
Mangle de la conexi\’on SIP
Los paquetes SIP permiten conectar desde los clientes SIP (teléfonos) a la centralita.
Aquí marcamos la conexión porque es más eficiente para marcar después los paquetes.
Para identificar el tráfico SIP buscamos los paquetes que van a la centralita así como los que vuelven desde ella usando el puerto 5060 (el puerto SIP por defecto).
/ip firewall mangle
add chain=forward dst-address=192.168.1.246 protocol=tcp dst-port=5060\
action=mark-connection new-connection-mark=sip-connection
/ip firewall mangle
add chain=forward src-address=192.168.1.246 protocol=tcp src-port=5060\
action=mark-connection new-connection-mark=sip-connection-out
Mangle de los paquetes SIP
Ahora ya podemos, a partir de las conexiones marcar cada uno de los paquetes.
/ip firewall mangle
add action=mark-packet chain=forward connection-mark=sip-connection new-packet-mark=SIP
/ip firewall mangle
add action=mark-packet chain=forward connection-mark=sip-connection-out new-packet-mark=SIP
Mangle de la conexion RTP
Los paquetes RTP permiten conectar la centralita al exterior (trunk).
Aquí marcamos la conexión porque es más eficiente para marcar después los paquetes.
Para identificar el tráfico RTP buscamos los paquetes que van a la centralita así como los que vuelven desde ella usando los puertos desde 10000 hasta 20000 (puertos RTP que se emplean por defecto) en UDP.
/ip firewall mangle
add action=mark-connection chain=forward dst-address=192.168.1.246\
new-connection-mark=rtp-connection port=10000-20000 protocol=udp
/ip firewall mangle
add action=mark-connection chain=forward src-address=192.168.1.246\
new-connection-mark=rtp-connection-out port=10000-20000 protocol=udp
Mangle de los paquetes RTP
Ahora ya podemos, a partir de las conexiones marcar cada uno de los paquetes.
add action=mark-packet chain=forward connection-mark=rtp-connection new-packet-mark=RTP
add action=mark-packet chain=forward connection-mark=rtp-connection-out new-packet-mark=RTP
Cambio del DSCP
En teorí el dscp dentro de una red interna dará más prioridad a nuestro tráfico (útil si este tuviera que viajar por varios switches locales).
/ip firewall mangle
add action=change-dscp chain=postrouting disabled=no packet-mark=SIP new-dscp=46
/ip firewall mangle
add action=change-dscp chain=postrouting disabled=no packet-mark=RTP new-dscp=46
Tag prioridad de vlan
Forzaremos la prioridad 5 de IEEE 802.1p para los paquetes que saquemos por la vlan de Orange.
Obviamente sólo afectará a los que salgan al exterior desde la centralita usando los puertos de RTP (recordemos que es el tráfico que va desde la centralita al trunk).
La prioridad 5 se suele usar para VoIP según el estándar de IEEE 802.1p.
/ip firewall mangle
add action=set-priority chain=output src-address=192.168.1.246\
new-priority=5 port=10000-20000 protocol=udp out-interface=ether24-vlan832
Colas de prioridad
Nosotros tenemos 300 Mbps de subida y 300 Mbps de bajada.
Nuestra salida a Internet es a través de la interfaz ether24-vlan832.
Nuestra interfaz que se usa para conectar a todas las bocas es: ether1-master . En esa interfaz limitaremos la descarga.
Dada la bibliografía todo apunta a que por llamada VoIP se necesita:
- 88 kbps para RTP
- 65 kbps para SIP
Nosotros tenemos dos líneas VoIP así que no necesitaríamos más.
Pondremos 100 kbps para tener margen y supondremos que queremos 6 llamadas en paralelo para el día de mañana.
Así necesitaríamos:
6 llamadas x ( 100 kbps + 100 kbps ) = 1200 kbps
Del total: 300 Mbps = 307200 kbps repartiríamos:
- Subida para VoIP: 1200 kbps
- Subida para VoIP: 306000 kbps
Para la descarga o bajada realizaremos las mismas suposiciones que para la subida.
Cola padre de subida
En todos estos sistemas de priorización o limitación del ancho de banda tenemos que crear una limitación padre que contenga el 100% de nuestro ancho de banda. Yo he puesto el 100% porque nunca lo vamos usar aunque se recomienda usar el 80% de lo que realmente te dan por no tener problemas (el 20% se suele ir protocolos).
Así pues limitamos la subida a 300 mbps y a la mínima prioridad por defecto.
/queue tree
add limit-at=300M max-limit=300M name=subida parent=ether24-vlan832 priority=8 queue=default
Cola de subida RTP con prioridad 1
Las 6 llamadas simultaneas consumiendo RTP serían: 6 x 100 kbps = 600 kbps .
Gracias al marcado anterior de los paquetes con la marca RTP podemos con el limit-at reservarles 600 kbps sólo para ellos.
/queue tree
add limit-at=600k max-limit=600k name=subida_pri_1\
packet-mark=RTP parent=subida priority=1 queue=default
Cola de subida SIP con prioridad 2
Las 6 llamadas simultaneas consumiendo SIP serían: 6 x 100 kbps = 600 kbps .
Gracias al marcado anterior de los paquetes con la marca SIP podemos con el limit-at reservarles 600 kbps sólo para ellos.
/queue tree
add limit-at=600k max-limit=600k name=subida_pri_2\
packet-mark=SIP parent=subida priority=2 queue=default
Cola de subida para resto de tráfico
Este tráfico (el resto) tiene la prioridad mínima: 8.
No usamos limit-at porque no tenemos por qué garantizar este ancho de banda.
/queue tree
add max-limit=306000k name=subida_pri_8\
packet-mark=no-mark parent=subida priority=8 queue=default
Cola padre de bajada
Aplican las mismas explicaciones que se dieron para las colas de subida.
/queue tree
add limit-at=300M max-limit=300M name=bajada parent=ether1-master priority=8 queue=default
Cola de bajada RTP con prioridad 1
Las 6 llamadas simultaneas consumiendo RTP serían: 6 x 100 kbps = 600 kbps
/queue tree
add limit-at=600k max-limit=600k name=bajada_pri_1\
packet-mark=RTP parent=bajada priority=1 queue=default
Cola de bajada SIP con prioridad 2
/queue tree
add limit-at=600k max-limit=600k name=bajada_pri_2\
packet-mark=SIP parent=bajada priority=2 queue=default
Cola de bajada para resto de tráfico
Este tráfico tiene la prioridad mínima: 8.
No usamos limit-at porque tenemos por qué garantizar este ancho de banda.
/queue tree
add max-limit=306000k name=bajada_pri_8 packet-mark=no-mark parent=bajada priority=8 queue=default
Bibliografía
Referencia – Todos los comandos de VoIP
/ip firewall mangle
#
add chain=forward dst-address=192.168.1.246 protocol=tcp dst-port=5060\
action=mark-connection new-connection-mark=sip-connection
add chain=forward src-address=192.168.1.246 protocol=tcp src-port=5060\
action=mark-connection new-connection-mark=sip-connection-out
add action=mark-packet chain=forward connection-mark=sip-connection new-packet-mark=SIP
add action=mark-packet chain=forward connection-mark=sip-connection-out new-packet-mark=SIP
add action=mark-connection chain=forward dst-address=192.168.1.246\
new-connection-mark=rtp-connection port=10000-20000 protocol=udp
add action=mark-connection chain=forward src-address=192.168.1.246\
new-connection-mark=rtp-connection-out port=10000-20000 protocol=udp
add action=mark-packet chain=forward connection-mark=rtp-connection new-packet-mark=RTP
add action=mark-packet chain=forward connection-mark=rtp-connection-out new-packet-mark=RTP
add action=change-dscp chain=postrouting disabled=no packet-mark=SIP new-dscp=46
add action=change-dscp chain=postrouting disabled=no packet-mark=RTP new-dscp=46
# IEEE 802.1p : Prioridad 5 al salir a Internet
add action=set-priority chain=output src-address=192.168.1.246 new-priority=5\
port=10000-20000 protocol=udp out-interface=ether24-vlan832
/queue tree
add limit-at=300M max-limit=300M name=subida parent=ether24-vlan832 priority=8 queue=default
add limit-at=600k max-limit=600k name=subida_pri_1\
packet-mark=RTP parent=subida priority=1 queue=default
add limit-at=600k max-limit=600k name=subida_pri_2\
packet-mark=SIP parent=subida priority=2 queue=default
add max-limit=306000k name=subida_pri_8 packet-mark=no-mark parent=subida priority=8 queue=default
add limit-at=300M max-limit=300M name=bajada parent=ether1-master priority=8 queue=default
add limit-at=600k max-limit=600k name=bajada_pri_1\
packet-mark=RTP parent=bajada priority=1 queue=default
add limit-at=600k max-limit=600k name=bajada_pri_2\
packet-mark=SIP parent=bajada priority=2 queue=default
add max-limit=306000k name=bajada_pri_8 packet-mark=no-mark parent=bajada priority=8 queue=default
Extra – Sniffer para evaluar calidad
Lo suyo es realizar este paso antes y despues de aplicar el QoS de VoIP (con diferentes file-name) para evaluar su impacto.
/tool sniffer
set memory-limit=2048KiB
set file-name=voip-evaluar01.pcap
set filter-ip-address=192.168.1.246
start
# Realizar llamada
stop
# Obtener voip-evaluar01.pcap
# por scp
Usar Common VoIP problems, How to detect, correct and avoid them. by Penny Tone LLC para interpretar el jitter.
Nuestro objetivo ideal es obtener, en base a los requisitos de VoIP:
Perdida de paquetes: Menos del 5%.
Latencia: Menos de 120-150 ms en un sentido.
Jitter (Buffer menos de entre 1 o 3 ms).
Referencia – Configuración Mikrotik – Dump inicial
# oct/30/2017 21:52:39 by RouterOS 6.35.4
# software id = LLYC-IDAG
#
/interface ethernet
set [ find default-name=ether1 ] name=ether1-master
set [ find default-name=ether2 ] mac-address=E0:51:63:04:C6:32
set [ find default-name=ether3 ] master-port=ether1-master
set [ find default-name=ether4 ] master-port=ether1-master
set [ find default-name=ether5 ] master-port=ether1-master
set [ find default-name=ether6 ] master-port=ether1-master
set [ find default-name=ether7 ] master-port=ether1-master
set [ find default-name=ether8 ] master-port=ether1-master
set [ find default-name=ether9 ] master-port=ether1-master
set [ find default-name=ether10 ] master-port=ether1-master
set [ find default-name=ether11 ] master-port=ether1-master
set [ find default-name=ether12 ] master-port=ether1-master
set [ find default-name=ether13 ] master-port=ether1-master
set [ find default-name=ether14 ] master-port=ether1-master
set [ find default-name=ether15 ] master-port=ether1-master
set [ find default-name=ether16 ] master-port=ether1-master
set [ find default-name=ether17 ] master-port=ether1-master
set [ find default-name=ether18 ] master-port=ether1-master
set [ find default-name=ether19 ] master-port=ether1-master
set [ find default-name=ether20 ] master-port=ether1-master
set [ find default-name=ether21 ] master-port=ether1-master
set [ find default-name=ether22 ] master-port=ether1-master
set [ find default-name=ether23 ] master-port=ether1-master
set [ find default-name=sfp1 ] master-port=ether1-master
/interface vlan
add interface=ether2 name=ether2-vlan832 vlan-id=832
add interface=ether24 name=ether24-vlan832 vlan-id=832
/ip pool
add name=dhcp_pool1 ranges=192.168.1.30-192.168.1.250
add name=dhcp_pool2 ranges=192.168.99.2
/ip dhcp-server
add address-pool=dhcp_pool1 disabled=no interface=ether1-master lease-time=3d \
name=dhcp1
add address-pool=dhcp_pool2 disabled=no interface=ether24-vlan832 lease-time=\
3d name=dhcp2
/interface ethernet switch port
set 0 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 1 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 2 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 3 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 4 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 5 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 6 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 7 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 8 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 9 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 10 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 11 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 12 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 13 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 14 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 15 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 16 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 17 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 18 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 19 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 20 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 21 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 22 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 23 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 24 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 25 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
/ip address
add address=192.168.1.1/24 interface=ether1-master network=192.168.1.0
/ip dhcp-client
add dhcp-options=hostname,clientid disabled=no interface=ether2-vlan832
/ip dhcp-server network
add address=192.168.1.0/24 dns-server=62.36.225.150,62.37.228.20 gateway=\
192.168.1.1
add address=192.168.99.0/24 gateway=192.168.99.1
/ip firewall filter
add chain=input comment="defconf: accept ICMP" protocol=icmp
add chain=input comment="defconf: accept established,related" \
connection-state=established,related
add action=drop chain=input comment=\
"Drop de todo lo que viene desde nuestra WAN" in-interface=ether2-vlan832
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related
add chain=forward comment="defconf: accept established,related" \
connection-state=established,related
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"Drop de todo lo que viene de la WAN que no esta DSTNATed" \
connection-nat-state=!dstnat connection-state=new in-interface=\
ether2-vlan832
/ip firewall nat
add action=masquerade chain=srcnat out-interface=ether2-vlan832
/ip service
set telnet disabled=yes
set www disabled=yes
set api disabled=yes
set winbox disabled=yes
set api-ssl disabled=yes
/system clock
set time-zone-name=Asia/Jakarta
/system routerboard settings
set protected-routerboot=disabled
Referencia – Configuración Mikrotik final
# nov/04/2017 00:03:10 by RouterOS 6.35.4
# software id = LLYC-IDAG
#
/interface ethernet
set [ find default-name=ether1 ] name=ether1-master
set [ find default-name=ether2 ] mac-address=E0:51:63:04:C6:32
set [ find default-name=ether3 ] master-port=ether1-master
set [ find default-name=ether4 ] master-port=ether1-master
set [ find default-name=ether5 ] master-port=ether1-master
set [ find default-name=ether6 ] master-port=ether1-master
set [ find default-name=ether7 ] master-port=ether1-master
set [ find default-name=ether8 ] master-port=ether1-master
set [ find default-name=ether9 ] master-port=ether1-master
set [ find default-name=ether10 ] master-port=ether1-master
set [ find default-name=ether11 ] master-port=ether1-master
set [ find default-name=ether12 ] master-port=ether1-master
set [ find default-name=ether13 ] master-port=ether1-master
set [ find default-name=ether14 ] master-port=ether1-master
set [ find default-name=ether15 ] master-port=ether1-master
set [ find default-name=ether16 ] master-port=ether1-master
set [ find default-name=ether17 ] master-port=ether1-master
set [ find default-name=ether18 ] master-port=ether1-master
set [ find default-name=ether19 ] master-port=ether1-master
set [ find default-name=ether20 ] master-port=ether1-master
set [ find default-name=ether21 ] master-port=ether1-master
set [ find default-name=ether22 ] master-port=ether1-master
set [ find default-name=ether23 ] master-port=ether1-master
set [ find default-name=sfp1 ] master-port=ether1-master
/interface vlan
add interface=ether2 name=ether2-vlan832 vlan-id=832
add interface=ether24 name=ether24-vlan832 vlan-id=832
/ip pool
add name=dhcp_pool1 ranges=192.168.1.30-192.168.1.250
add name=dhcp_pool2 ranges=192.168.99.2
/ip dhcp-server
add address-pool=dhcp_pool1 disabled=no interface=ether1-master lease-time=3d \
name=dhcp1
add address-pool=dhcp_pool2 disabled=no interface=ether24-vlan832 lease-time=\
3d name=dhcp2
/queue tree
add limit-at=300M max-limit=300M name=subida parent=ether24-vlan832 queue=\
default
add limit-at=600k max-limit=600k name=subida_pri_1 packet-mark=RTP parent=\
subida priority=1 queue=default
add limit-at=600k max-limit=600k name=subida_pri_2 packet-mark=SIP parent=\
subida priority=2 queue=default
add max-limit=306M name=subida_pri_8 packet-mark=no-mark parent=subida queue=\
default
add limit-at=300M max-limit=300M name=bajada parent=ether1-master queue=\
default
add limit-at=600k max-limit=600k name=bajada_pri_1 packet-mark=RTP parent=\
bajada priority=1 queue=default
add limit-at=600k max-limit=600k name=bajada_pri_2 packet-mark=SIP parent=\
bajada priority=2 queue=default
add max-limit=306M name=bajada_pri_8 packet-mark=no-mark parent=bajada queue=\
default
/interface ethernet switch port
set 0 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 1 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 2 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 3 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 4 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 5 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 6 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 7 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 8 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 9 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0:\
8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 10 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 11 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 12 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 13 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 14 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 15 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 16 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 17 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 18 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 19 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 20 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 21 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 22 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 23 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 24 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
set 25 per-queue-scheduling="wrr-group0:1,wrr-group0:2,wrr-group0:4,wrr-group0\
:8,wrr-group0:16,wrr-group0:32,wrr-group0:64,wrr-group0:128"
/ip address
add address=192.168.1.1/24 interface=ether1-master network=192.168.1.0
/ip dhcp-client
add dhcp-options=hostname,clientid disabled=no interface=ether2-vlan832
/ip dhcp-server network
add address=192.168.1.0/24 dns-server=62.36.225.150,62.37.228.20 gateway=\
192.168.1.1
add address=192.168.99.0/24 gateway=192.168.99.1
/ip firewall filter
add chain=input comment="defconf: accept ICMP" protocol=icmp
add chain=input comment="defconf: accept established,related" \
connection-state=established,related
add action=drop chain=input comment=\
"Drop de todo lo que viene desde nuestra WAN" in-interface=ether2-vlan832
add action=fasttrack-connection chain=forward comment="defconf: fasttrack" \
connection-state=established,related
add chain=forward comment="defconf: accept established,related" \
connection-state=established,related
add action=drop chain=forward comment="defconf: drop invalid" \
connection-state=invalid
add action=drop chain=forward comment=\
"Drop de todo lo que viene de la WAN que no esta DSTNATed" \
connection-nat-state=!dstnat connection-state=new in-interface=\
ether2-vlan832
/ip firewall mangle
add action=mark-connection chain=forward dst-address=192.168.1.246 dst-port=\
5060 new-connection-mark=sip-connection protocol=tcp
add action=mark-connection chain=forward new-connection-mark=\
sip-connection-out protocol=tcp src-address=192.168.1.246 src-port=5060
add action=mark-packet chain=forward connection-mark=sip-connection \
new-packet-mark=SIP
add action=mark-packet chain=forward connection-mark=sip-connection-out \
new-packet-mark=SIP
add action=mark-connection chain=forward dst-address=192.168.1.246 \
new-connection-mark=rtp-connection port=10000-20000 protocol=udp
add action=mark-connection chain=forward new-connection-mark=\
rtp-connection-out port=10000-20000 protocol=udp src-address=\
192.168.1.246
add action=mark-packet chain=forward connection-mark=rtp-connection \
new-packet-mark=RTP
add action=mark-packet chain=forward connection-mark=rtp-connection-out \
new-packet-mark=RTP
add action=change-dscp chain=postrouting new-dscp=46 packet-mark=SIP
add action=change-dscp chain=postrouting new-dscp=46 packet-mark=RTP
add action=set-priority chain=output new-priority=5 out-interface=\
ether24-vlan832 port=10000-20000 protocol=udp src-address=192.168.1.246
/ip firewall nat
add action=masquerade chain=srcnat out-interface=ether2-vlan832
/ip service
set telnet disabled=yes
set www disabled=yes
set api disabled=yes
set winbox disabled=yes
set api-ssl disabled=yes
/system clock
set time-zone-name=Asia/Jakarta
/system routerboard settings
set protected-routerboot=disabled